In spite of the move toward living digitally, Americans still use over 90 million tons of paper each year. Everyone nowadays seems to be reading everything online, and yet more than 2 billion books are printed each year. In addition, over 24 billion newspapers are printed annually, along with 350 million magazines. Only about half the available waste paper is recycled each year, leaving the other half to end up in local dumps and waterways.
Of course, much of this wasted paper originates from commercial enterprises, such as offices, publishers, schools, colleges, and manufacturing. The average consumer has cut way back on their personal paper usage.
Saving Trees
You may have learned this stuff in grade school but forgotten it. Trees make oxygen, the air we breathe. They filter out harmful pollutants. They also produce foods like maple syrup, walnuts, pecans, and almost all fruits. A tree has its own self-replicating technology: it drops seeds each year so that new trees can be born. Many birds and small animals call a tree their home.
When we slash and burn a rainforest, we do irreparable harm to our planet. Rainforests are precious and delicate eco-systems that are simply remarkable on every level. There’s no way for humans to cheaply create, build or invent the machine that does what one common oak tree does. These are just a few of the reasons why it’s so important to save every tree possible. By taking strong actions now, we can ensure that our grandchildren will be able to walk through a lovely forest of aspens or look out on a field of evergreen trees and smell that unmistakable essence of evergreen.
Saving Other Resources
Each time someone prints something, there is other waste involved. You can’t print out a letter without using ink. You also need electricity. In the end, there are numerous direct and indirect costs associated with printing anything. And there are always harmful effects to the environment, such as the pollution caused by a single paper mill. When you add it all up, the cost to print a book includes damage to the eco-system, waste of natural resources, and it adds to the landfills. Instead, let’s all look for ways to reduce our paper usage so we can save as many trees as possible. We begin with these seven timely suggestions.
One: Recycle Phone Books
In this day and age, very few people use a phone book, yet most cities still print them. They are rarely recycled, but it’s possible to save approximately 30 trees simply by recycling 500 phone books of average size. Each year, when the new phone books arrive, be sure to throw the old ones in your recycling bin. These items can be recycled just like any other paper product. There’s nothing hard or complicated about the process. Most of us simply forget.
Two: Opt Out of Junk Mail
Many of us can fill a trash can with the junk mail we get in just one week. It’s time-consuming to open all those letters, plus it’s wasteful. Simply opt out. You can stop receiving certain emails, but many people are not aware that you can also do this with printed junk mail. It’s dangerous in this day and time to allow companies to send you pre-approved credit card applications through the mail. These can be stolen and used by thieves to obtain credit cards in your name.
The consumer reporting companies maintain a website and a toll-free number that consumers can call to opt out of receiving these offers. Simply by calling the toll-free number, you can opt out for five years. If you’d like to stop receiving junk mail permanently, then you must go to the website. The process is a bit more complicated but still worth it.
Three: Go Paperless
Many people have already done this, but it’s simple to go paperless at your bank and all creditors. Since it’s much cheaper for businesses to send your statements and bills by email, most companies make it very simple to choose “go paperless”. Go to their website and look for information about this on the homepage. Usually, you need to log into your account and then set up the paperless option there. It’s normally just a matter of a few clicks and you’re all done.
Four: Stop Printing So Much
The average consumer has a much better handle on this concept than the average business. Most homeowners barely use their printer these days. At the office, it’s a totally different story. The average office still prints out reports, surveys, journals, meeting notes and many other items. When you do need to print something out, you can easily adjust margins to .75 inch and thereby get more writing on each page. This reduces the number of pages on every document.
Five: Sign Up for Online Magazines
Who among us has a dusty pile of old magazines somewhere in our home? This is quite a common problem. You can eliminate this problem by signing up for online magazines. When you think about it, online publications make more sense. Once a document is digitized, you can quickly search through it for information. We’ve all read something interesting that we wanted to go back and look at again, but just can’t find the correct book or magazine. It’s easy to search through digital documents of any length using a single keyword and find exactly what you’re looking for. If you’re one of those people who hate to throw away old magazines, this is the perfect solution. Just choose digital publications from now on.
Six: Use Electronic Storage
Occasionally, we all get receipts, instructions, forms, and other important documents that we need to save. It’s very easy now to snap a photo of these types of items and then store them on your hard drive. You can create files specifically for warranties, receipts, or whatever it is. There are a number of handy apps now available that can make this even more convenient to use. Once you get these copies on your computer or phone, they can be saved by the date or type of item. This is much better than having a shoebox full of old receipts lying around gathering dust.
Seven: Buy Recycled Stuff
Recycled items are good for the environment. Because of the lower costs involved, you can now purchase countless recycled items that you use every day. These products include paper plates, envelopes, greeting cards, books, notebooks, household paper products and others.
The average person simply doesn’t think to look for this on the packaging. These recycled items are for sale on the shelf, right alongside products of the same type. It’s just a matter of looking for the phrase, “Made from Recycled Materials”.
Tips for Success
Sometimes we all receive important papers and worry that we’ll lose or misplace them. This happens with printed documents as well as digital items. To keep track of your important papers at home or at the office, purchase a small filing cabinet. For each topic or item, create a single file folder. You can include the date and any other important information like PIN numbers or due dates.
Saving digital documents is simple too. If you have a word processing program like Microsoft Word, be sure to save these items to your hard drive. If you already have too much on your hard drive, programs like Google Docs allow you to store everything in the cloud. A number of companies have created apps and software for saving important documents. It’s just a matter of finding the program that works best for you.
Of course, it goes without saying that we should all back up our phones and computers on a regular basis. It can be helpful to have a few blank thumb drives lying around for this purpose. Blank DVDs are cheap and you can store from 4.7 GB to 9.4 GB. These disks can last for years but be sure to stick them in a paper sleeve so they aren’t accidentally scratched. No paper sleeves available? Plastic lunch bags work perfectly.
Electronic document collaboration is superior to paper document collaboration. Here at Vision of Earth, we use Google Docs for all of our writing. It is a simple system that allows us to cooperatively edit documents, as well as track the changes made by each person. For more information on how we at collaborate, see our post on software tools that we use to collaborate across the world.
It is possible to do effective editing and collaboration even using standard word processors. For instance, you can learn to use “track changes” in Microsoft Word, or Edit->Changes in OpenOffice Writer. This lets you put editing marks in documents, and also view the editing changes that have been made by other people.
Use email (electronic mail) rather than paper mail when you can. Most businesses and even governments are in the process of transferring over to electronically available services. This will drastically reduce the costs of postal service as well.
Use a USB stick, also known as a ‘thumb drive’, to move around or share electronic documents rather than printing them. Encourage people coming to meetings to bring their reports in electronic format, and for attendees to bring electronic storage of their own (or share via an Internet-based document storage). Many companies are utilizing an ‘intranet’ now, allowing them to securely distribute documents to company employees only.
Use electronic fax services. There are a number of them available, some of which are even free for one-page faxes such as fax zero. The quality can sometimes be a bit low with the free services, so it is recommended that you phone the fax receiver to make sure that they can read the sent document.
Don’t place paper contacts on business cards (such as a postal mailing address). Only put email, and phone. This forces people to contact you through these electronic mediums.
Home
Use cloth napkins.
Use rags instead of paper towels.
Try to not use paper plates. Use durable washable ones if you need something for a BBQ. In terms of environmental impact, the trend usually goes like this: Reusable plates are better than paper plates which are better than plastic plates.
Use a handkerchief instead of kleenex.
Use a whiteboard for lists/notes/announcements.
Buy bulk foods using your own reusable containers rather than buying supermarket boxed
How Much Paper Does Your Office Use Each Year? Tips For Reducing Paper Use
Are you an average worker? If so, statisticians say you use around 10,000 sheets of paper every year.
If that sounds like a lot, that’s because it is. The bottom line is that the average American worker uses way too much paper. To put it in perspective, here are some facts to consider:
4 billion trees are cut down each year to make paper
16% of landfill solid waste is comprised of paper
In one year, the average American citizen will consume 800 million pounds of paper
If you’re having a hard time visualizing how much paper that really is, imagine 5.5 million printed copies of the Hunger Games Trilogy. In terms of trees, you would have to cut down every tree in New York City’s Central Park, or enough trees to build a city with 25,000 houses.
No Office Is Alike
The real issue is how that paper is being used or, in this case, not used. According to a recent survey, 70% of the total waste in offices is made up of paper and as much as 30% of print jobs are never even picked up from the printer. Even worse, 45% of printed paper ends up in the trash by the end of the day. When you consider that the total amount spent annually by U.S. companies on printed documents is $120 million, it’s clear that there is a lot of pointless printing in modern offices (and a lot of wasted money).
Of course, no one is an average worker and there is no such thing as an average office.
I recently visited a small startup that operated out of two different offices. In one office, the company’s engineering team does the coding and support for a Cloud-based software system. These workers are coding all day and hardly ever speak to one another — that’s done on chat — and they almost never print anything. The lead programmer could barely understand why he needed a printer at all and was satisfied with an inexpensive multifunction machine.
Meanwhile, in the same company’s main office, marketing, sales and support staff had multiple printers running all day to publish reports, marketing materials, and more, and stacks of unread documents ended up being piled in bins next to the machines. These are two very different offices within the same company with very different needs: one office barely needed a printer while the other was in desperate need of a Managed Print solution.
It might surprise you to know that even though we sell and service printers, we want you to print less.
Reducing paper usage isn’t just good for business; it’s good for the planet. Take a look around the office. What do you see?
Reams of wasted paper in the recycling bin?
No strategic supply management process?
Underutilized or inefficient printers?
Color copies that should be printed in black and white?
If that sounds familiar, then you need to manage your printers more effectively. We recommend a three-step approach to designing a print strategy that eliminates wasteful printing and matches your business needs.
Evaluate your device use, output, supplies, and viability to align them with a purchasing process
Integrate best-of-class software and printer hardware into your current system
Continuously assess your consumption based on actual usage — because it will always be in flux
Managed Print is ideal for controlling costs and can help ensure that your machines are helping you better serve your clients. To see how such a print partnership can benefit your company, download the Major Signs You Need Managed Print infographic below.
How much paper can be made from one tree?
It is impossible to specify how much paper can be made from one tree, due to its complicated process and multiple factors which impact production. However, if we assume that the following paper products have been produced using 100 percent hardwood. A cord of wood is approximately 8 feet wide, 4 feet deep, and 4 feet high. A cord of air-dried, dense hardwood (oak, hickory, etc.) weighs roughly 2 tons, about 15-20 percent of which is water.
It has been estimated that one cord of this wood will yield one of these approximate quantities of products:
- 1,000-2,000 pounds of paper (depending on the process)
- 942 100-page, hard-cover books
- 61,370 No. 10 business envelopes
- 4,384,000 commemorative-sized postage stamps
- 460,000 personal checks
- 1,200 copies of National Geographic
- 2,700 copies of an average daily newspaper
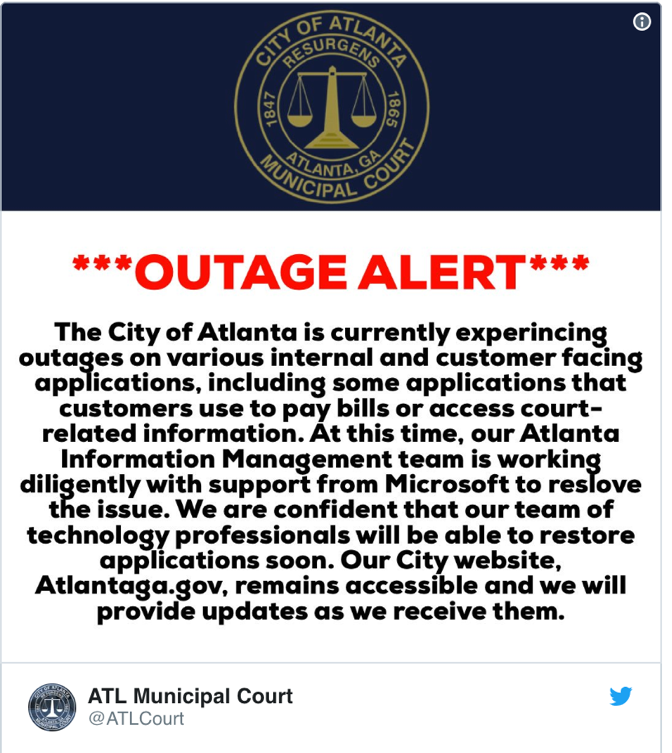
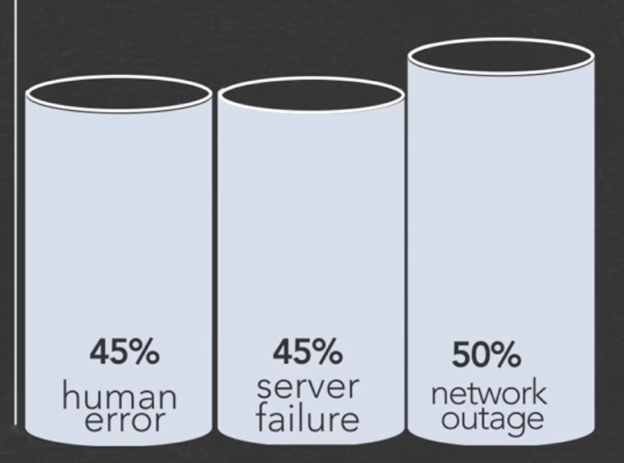
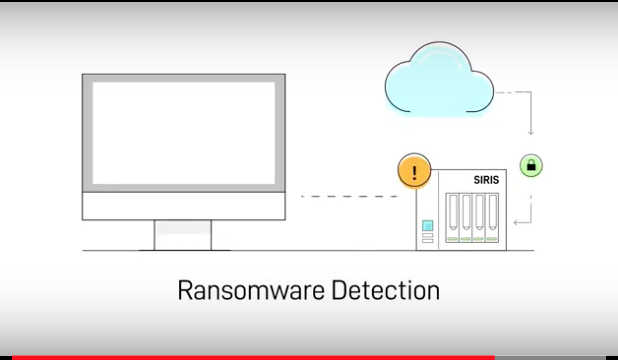
 Many U.S. and Canadian businesses, even large enterprises, don’t always plan ahead and, instead, operate in a reactionary mode. Security professionals in the U.S. and Canada are concerned–The mandatory 72-hour GDPR breach-notification period has them worried because they don’t think most businesses are prepared. The U.S. doesn’t have a national data-breach notification requirement. However, most states do require notification within 30 to 45 days. If businesses don’t comply, they will be fined 4% of their global revenue up to $20 million. Plus, the consumers whose data is breached can file class-action suits against them for noncompliance.
Many U.S. and Canadian businesses, even large enterprises, don’t always plan ahead and, instead, operate in a reactionary mode. Security professionals in the U.S. and Canada are concerned–The mandatory 72-hour GDPR breach-notification period has them worried because they don’t think most businesses are prepared. The U.S. doesn’t have a national data-breach notification requirement. However, most states do require notification within 30 to 45 days. If businesses don’t comply, they will be fined 4% of their global revenue up to $20 million. Plus, the consumers whose data is breached can file class-action suits against them for noncompliance.