Small and mid-sized companies have a tendency to operate under the assumption that hackers target only more extensive operations. There’s a simple logic to that misconception that these criminals instigate cyber breaches that reap the highest possible reward. Nothing could be further from the truth.
Check out what Robert Herjavec and Scott Schober have to say on Cybersecurity.
Click Here

While hacks into the Democratic National Committee and Equifax make big headlines, the majority of cyber attacks are carried out on smaller, vulnerable systems. Most hackers merely look for the low hanging fruit. If your small or mid-sized company has modestly valuable data and lacks top-tier cybersecurity, you are that low hanging fruit.
By 2020, upwards of 6 billion people globally and 283 million Americans are expected to utilize the Internet. That means businesses of every level will be fully engaged and it only takes two miscreants on another continent to breach your security.
Cybercrime has already reportedly outpaced the combined profits of all the major drug cartels in the world at $6 trillion annually. Unlike vast criminal organizations, two computer whizzes with laptops thousands of miles away can extract sensitive information without a company even knowing until it’s too late.
These days, stealing credit card info is not among the highest priorities. Cybercriminals have discovered that personal and personnel information can yield significant paydays. If you still don’t think cybersecurity ranks among the highest priorities for small and mid-sized companies, just listen to this.
Hacks Are Often Inside Jobs
It may seem counterintuitive, but a company’s most significant cyber threat can be found among the most valued employees. Staff members are not generally acting in a nefarious fashion. In fact, loyal employees are often just that, loyal. But a pervasive attitude exists in workplaces that checking in on personal social media, using various non-work related apps and platforms is both allowable and safe.
According to cyber security experts, upwards of 93 of all breaches that are investigated thoroughly trail back to an employee. Although that person is generally not the so-called “inside man” or “inside woman” regarding criminal intent, their nonchalant attitude about checking personal sites exposed the small or mid-sized organization to a massive data breach.
Many are merely duped by phishing scams or inadvertently infest a business system with malware. This could occur by synching an unsecured device, moving data on a USB drive back and forth between home and work, or surfing the Internet among other security missteps. While many business decision-makers believe their data is not at risk, it takes a cybersecurity professional to build a company-specific “human firewall” that reduces internal threats through actionable policies and training.
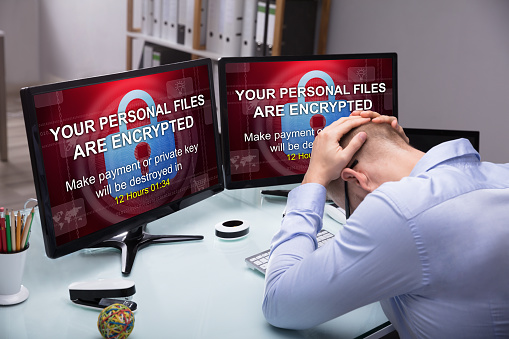
Small And Mid-Sized Organizations Held Hostage Everyday
No Third World drug cartel can compare to the volume of theft leveled by small-time hackers. Ransomware remains the top malicious software and ranks among the most lucrative type of cyberattack. This variety of malware targets business systems by penetrating them through a camouflage method of encryption. Once inside a business’ network, it quickly encrypts critical data and makes everything inaccessible to the organization.
The name “ransomware” was earned by what comes after. A defiled organization will likely get a notice to pay a certain amount — often in bitcoin — to get an encryption code allowing you to restore access to your own files. This hostage situation often proves fruitful for the cybercriminal because paying them off appears to be in the company’s best financial interest. Sadly, too many business leaders only move forward with advanced cybersecurity after suffering a feeling of helplessness and humiliation.
Underachieving Cybersecurity Protocols Prove Costly
A Verizon Data Breach Report reportedly concluded that upwards of 60 percent of all incursions during 2016 could be attributed to outside forces. These data breaches were considered instances of “hacking” by a third party’s intent to circumvent existing security measures. Hackers tend to seek out a company’s weakest cyber defense points to gain access.
In essence, this follows the adage that a chain is only as strong as its weakest link. Among the more notable instances of a weak-link failure was JP Morgan’s massive breach in 2014. Despite having a top-tier cybersecurity team in place, a single server was missed during a password update. That single under-protected server resulted in what was ranked among the top 10 worst cyber thefts in history. Approximately 83 million household and business accounts were reportedly impacted at a whopping $100 million.
While this level of cyber theft makes mainstream media headlines, hackers tend to have greater success penetrating smaller companies with far less sophisticated cyber security systems. The basic criminal business model relies on volume not occasional massive paydays. Think about it this way. The Brinks Job made bank-robbing history in 1950, but stick-up men knock off liquor stores every day.
Unpatched Security Bugs Attract Cybercrime Infestations
One of the more prevalent methods used by a hacker is to infiltrate your system in plain sight. Cyber thieves often use well-known software deficiencies commonly called bugs as a type of cracked door.
When software companies send out routine fixes such as patches, users have the option of making this repair. But when a system appears to be functioning appropriately, a small or mid-sized business may discard the effort as more of a nuisance than anything else. That could prove to be a fatal data breach mistake.
When systems linger unpatched, hackers may be quick to seize on specific vulnerabilities and infiltrate a company’s network. It’s important to understand that cybersecurity only seems like another time-consuming task that detracts from company goals. Anyone who uses computers, devices, software or accesses the Internet is inherently in the cybersecurity business. Without adequate cybersecurity systems, policies and protocols in place, the entire organization remains at risk.
Data Breaches Threats Represent A Clear And Present Danger
If you remain unconvinced about how crucial cybersecurity is to your business’ integrity, consider these telling facts. The U.S. government has placed the most significant emphasis on increasing only two areas of the military budget — special ops and cybersecurity.
Today, a person’s electronic medical records are more valuable than credit card information on the dark web. And, electronic ransoms are the fastest growing cybercrime and are expected to occur every 14 seconds by 2020. The question is no longer if a sub-par system will be hacked, it’s when