Downtime, compromised data, security breaches, and slow-running technology cause big headaches for today’s accountants. After all, you need your technology, and when it’s not working, every hour that goes by costs your firm money.
You can’t afford to sit idle—when your technology doesn’t work, neither do you. If your competitors use more efficient IT solutions, they’ll blow right past you and take your clients away. Or worse, your reputation will suffer.
Technology helps you carry out essential tasks, exercise professional judgment, engage with clients, provide advice, and settle tax issues. If you view technology as an opportunity rather than a threat, your firm will prosper and reap the rewards of your efforts. If you don’t, you’ll fall behind the competition.
You use technology now more than ever—at least, you should. Today’s technology is invaluable, and with time it will become even more so. In the past, the accounting profession lagged behind others in the adoption of new technology. They relied on paper-based filing and printed accounting forms that were time-consuming to process.
Accounting firms like yours have now embraced new technology. Just like other businesses, you need to streamline your services to save time and process accounting information. With modern technology like cloud-hosted accounting software, you and your clients can access data directly and simultaneously. The days of shuffling papers back and forth are over.
However, along with technology-provided benefits come some challenges.
Failed backups, slow-running email, application problems, and operating-system crashes create headaches that set up barriers to your success.
Downtime is a threat—it results in a significant loss of productivity. You can’t afford to be faced with server failures, poor systems performance, accidental file deletions, or software application crashes. Without access to your data, you and your employees can’t do your jobs. Money goes out the window, and you can’t meet your filing deadlines.
Data security is another issue that can cause significant headaches. Client confidentiality is your most important duty. But with hackers and intruders who want to infiltrate your technology for their own financial gain, your technology landscape is like a minefield unless it’s adequately protected.
As a Chartered Accountant, you are governed by Rules of Professional Conduct that always have and will continue to guarantee the privacy and confidentiality of your clients’ personal information. If their financial data is stolen, you’ll face penalties, fines, and possibly civil prosecution. You can’t take that chance.
THE ANSWER IS TO CONTRACT WITH THE RIGHT IT SERVICES PROVIDER.
To prevent IT headaches, you need service and support from an IT provider who understands the Line of Business (LOB) applications you use including your financial preparation and planning software and billing systems that keep your operations efficient.
The right provider can ensure these seamlessly incorporate with other applications you use like Microsoft Office or Office 365. When you have access to expertise from an IT Service Provider who truly understands your needs, you can effectively leverage these powerful tools.
Look for an IT Service Provider who has been serving the needs of accounting firms and corporate accounting departments for years. The best choice is one who can cover a broad range of technology requirements through both professional services and Managed IT Services and who can grasp the complexities your accounting firm faces.
They should be able to help you avoid IT headaches when automating routine accounting processes, sharing financial files, deploying mobility solutions, and capitalizing on tools like electronic filing.
Your accounting practice requires a complete technology management solution including data protection and proactive monitoring of all critical functions on your network, servers, and workstations. Plus, you should insist upon a fixed-cost solution with predictable budgeting. Just as your accountants are committed to your clients’ success, your IT Service Provider must be dedicated to making you successful and view themselves as an extension of your practice.
Your IT Service Provider should be adept with:
- Cloud Technologies that improve your productivity, efficiency, and security
With cloud solutions, you can eliminate the cost of paper and the hassle of sifting through files, store massive amounts of information (Big Data), share important files in real time and secure your clients’ information offsite in high-security data centres.
- Accounting Practice Management Software that helps you run day-to-day operations including the centralization of client data, tracking due dates, staffing, workflow management, automated billing, and time tracking
- Tax Preparation and Filing Software designed explicitly for accounting firms, so you can analyze different income tax scenarios and have access to the reporting tools you need for fast, easy reconciliation
THE WORST HEADACHES RESULT FROM IT SECURITY BREACHES.
Data breaches are increasing exponentially. Cyber mafias have set up in towns like yours, operating from legitimate-looking offices. Hackers are no longer kids in their parents’ basements working on a few computers. Cybercrime is an international and sophisticated business with cartels operating around the globe.
Your data is valuable, and your accounting firm is a target. You need the expertise of an IT Service Provider who stays up to date on the latest threats. It’s imperative that you protect client information. But IT security best practices change so rapidly that accounting firms often find themselves falling behind the curve. If you do, your firm is at risk of viruses, network vulnerabilities, and data breaches. This results in more than a headache; now, you’re looking at a migraine.
Criminals have many ways of stealing your data.
Internet Exploits
Your employees use connected devices to interact with, track, monitor, and simplify just about every area of their work and personal lives. However, these technologies also provide access to sensitive, confidential information and present a wide variety of new security issues for attackers to exploit.
Third-Party Attacks
Cybercriminals have learned that contractors and other third-party providers aren’t as secure as large vendors, and lower security provides a pathway into otherwise-secure networks. Examine who can connect to your network and access confidential information, even if you believe appropriate security measures are in place.
Social Media Attacks
Social media presents two main security headaches:
- A website you visit or service you use can be infected with malware that spreads until your network is ripe for a data breach. Malicious social media content is expected to grow 400 percent as attackers continue to distribute their malware and steal client data.
- A determined hacker or team can scrape social media sites to assemble a surprising amount of personal data very quickly. This data can be used to engineer an attack.
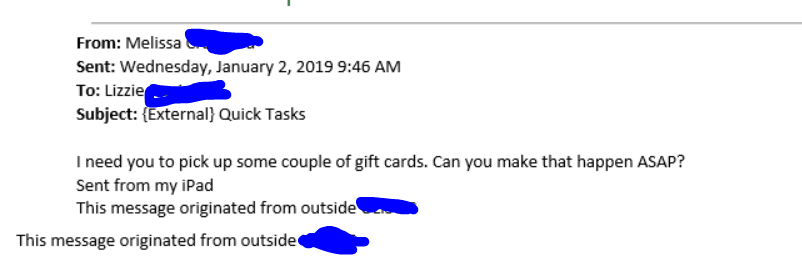
Social Engineering Attacks
Human nature is easily the weakest link in any security chain. Was that really a utility-company employee you held the door for this morning? Are your office painters propping open a secure entrance to make their task more manageable? Did your receptionist just give all your passwords and hers to someone who called claiming to be from tech support on another floor? Will your colleague’s curiosity causes him or her to insert the USB key “found” in the parking lot into a computer connected to your systems?
Mobile Malware Threats
Security experts have been warning us about mobile malware threats for a long time, and users have grown immune to these warnings. Mobile-device use is increasing, as is the sophistication of attacks. At the risk of being the boy who cried, “Wolf,” every year a major mobile malware attack is more likely to occur. Attackers typically select the most significant number of potential victims. So, they will target mobile devices, specifically Android and jailbroken iOS devices.
Sophisticated DDoS Attacks
Distributed Denial-of-Service attacks don’t directly steal your information. Instead, they overwhelm your site or service with so much traffic that it prevents legitimate users from connecting. These attacks have evolved beyond simple flooding of traffic. They probe and then morph, based on the defences in place on your network. Such advanced and sophisticated attacks can seriously impair your accounting firm’s operations.
TO PREVENT THESE SECURITY HEADACHES, YOU NEED A SECURITY PLATFORM WITH REMOTE-ACCESS MONITORING AND RELIABLE BACKUP AND DISASTER-RECOVERY SOLUTIONS.
Be sure your IT Service Provider implements innovative, up-to-date security measures to protect your accounting firm against intruders, malware threats, and disasters. And ensure they can do the following things
Ensure:
- You comply with accounting and confidentiality requirements when using technology.
- You use appropriate technical means to minimize the risks of disclosure, discovery, or interception of communications.
- Data and email are encrypted to protect your sensitive information.
- You adopt management practices that offer protection against disclosure or discovery of electronically transmitted messages.
Prevent:
- Unauthorized access to your electronic data
- Computer viruses from damaging your data
- Natural or manmade disasters from affecting your IT operations
Confirm:
- Your files are reliably backed up and recoverable.
- Both offsite and onsite data backups are maintained.
- Data is restorable by performing ongoing testing.
Provide:
- Systems Analysis
- Mobile Device Management
- Up-to-Date Security Solutions
- User Support and Training
Your IT Service Provider should implement a security platform with multiple layers of protection, with 24/7 remote monitoring to detect infections and intrusions, and block them before they get in and steal or hold your data hostage. Many accounting firms are unaware that this goes on. Your IT provider will keep you informed and train your staff to recognize threats, so you know what to do if one comes across your computer screen.
Your very most basic security solution should include barriers with virus and malware detection at the firewall level and DNS (Domain Name Server) controls to ensure your users don’t visit hijacked websites. Your employees should also utilize two-factor authentication access practices to prevent criminals from getting into your network.
Nothing is more important than protecting the information on your network and the peace of mind that comes from knowing you can fully recover if a disaster hits your firm. Your IT provider must ensure your business continuity and disaster recovery solutions will meet your objectives and must implement a robust backup and secure off-site replication solution.
While computer systems can easily be replaced, the intellectual property and sensitive information stored on those systems cannot. Computer hard drives can fail, laptops can be stolen or lost, and data can be erased due to human error or viruses. It’s important for your accounting firm to have a backup system to keep data safe and avoid data loss.
Ask your IT Service Provider if they employ system virtualization and a private cloud with a fully redundant system that can be replicated across multiple data centres. If your data is compromised or damaged, a new clone of your system and data can be spun up with a new, fresh image in a manner of seconds.
Be sure your IT provider uses an Intrusion Detection System. This will catch anything that may have bypassed your firewall. They can either be used to find a break-in attempt in progress or detect one after the fact. In the latter case, it’s too late to prevent any damage, but at least you’ll be aware of the problem.
If an intruder gets into your system, the first thing they typically do is install a “rootkit.” A rootkit is a script or set of scripts that can make changes to your IT system and hide in common system utilities. They function in the background without your knowing they are there. Criminals can easily obtain these on the Internet. This is one reason you must have reliable backups of your entire IT system. If rootkits are discovered, you’ll need to re-install your system and data and start over from scratch.
Your mobile devices also require monitoring and management. If a phone or laptop is stolen, you must be able to remotely wipe your confidential data. Mobile Device Management also prevents disgruntled employees from leaving with your confidential or proprietary data.
Your IT Service Provider should also employ encryption to protect your confidential data. They should encrypt both your emails and data files to ensure the security of information. Encryption can protect your data at rest, such as on laptops or portable servers, as well as data in motion, such as over wireless networks or the Internet.
One of the most overlooked security aspects in accounting firms is their creating and retaining policies regarding email and data. You are accountable for instituting and employing a strategy that details the duration over which your client data and emails will be stored and deleted. Ensure your IT provider can implement automated solutions to handle this.
IN CONCLUSION
You understand the unique challenges and technology demands your accounting firm faces. Whether your IT headaches come from the security risks of handling and storing confidential information or the difficulties of keeping up with new, innovative Line of Business Solutions, you need an IT Service Provider who can ease your struggles and your IT headaches.