Using 123456 as Your Password?
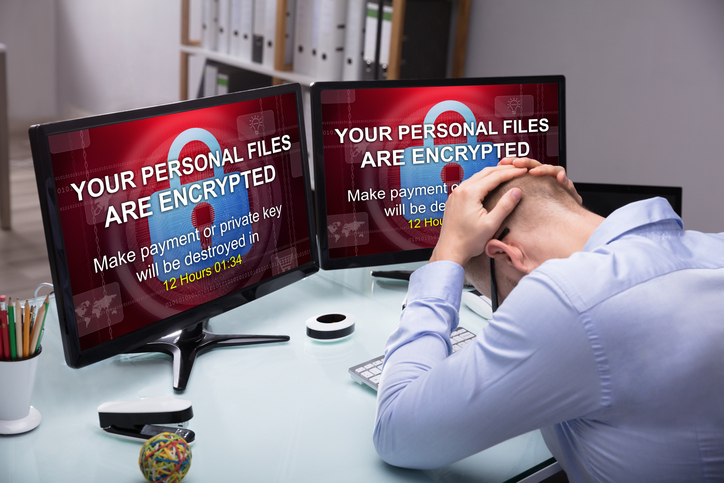
Is your company’s cybersecurity repeatedly swept under the rug? While reinforcing passwords and setting up firewalls can seem daunting, you may not realize the severe risk of neglecting these and other routine security practices. Unfortunately, as the Internet evolves to meet our needs and desires, the same can be said of malicious hackers and programs. Ill-intentioned parties are constantly becoming more adept at accessing private information and what is meant to remain secure data.
Despite this growing threat, many of today’s Internet users and company employees have not reacted accordingly to increasingly well-equipped hackers. In fact, a 2019 Forbes article cites that ‘123456’ remains the most commonly used Internet password in the US and the UK. By maintaining such basic passwords, cyber-intruders are granted easy access to personal or professional information, and quickly cash in your data for billions per year. It’s officially time to protect your business’ sensitive information and data. This article will detail the importance of ramping up your company’s cybersecurity measures as well as a few simple ways to get started. Discover the following achievable strategies to significantly decrease your company’s risk of hacking and intrusion.

Eliminate the “Not Much to Steal” Mentality
An extremely common line of reasoning within mid-size companies is that cyber hackers probably won’t bother taking advantage of them because “there’s not much to steal.” This statement could not be further from the truth and it tends to lure employees and leadership alike into a false sense of security. The fact remains that 43% of all cyberattacks are aimed at small businesses. Hackers can just as easily sell a smaller company’s information as they can a larger corporation’s. However, the major difference is that larger businesses tend to allocate funds to cybersecurity, whereas smaller or mid-size companies might not prioritize this cost. Many professionals hesitate over the cost of cybersecurity but may not consider the potentially catastrophic costs of not having it.
To remain vigilant, employees should keep an eye out for attachments from unknown accounts. These documents could be in the form of a Microsoft Office attachment that initially appears legitimate. As a rule of thumb, do not open emails or messages from accounts you’re not familiar with. Because it takes a company 6 months on average to discover a security breach, it is well worth your time to evaluate your company’s current cybersecurity situation and consider where there might be room for improvement.
Prioritize Employee Education
One of the easiest ways to head off potential security threats in your mid-size company is to thoroughly educate team members on cybersecurity practices and procedures. If there currently aren’t any, create and enforce protocols that can be communicated through online training, checklists, and seminars. Make sure to discuss the specificities of your company as it applies to Internet safety and data protection. Without this crucial step of employee education, your company will waste time and resources trying to rectify security issues that could have been resolved through open communication.
Keep in mind that cybersecurity is frequently evolving. Therefore, employees should be updated regularly on the best ways to protect company information. An easy measure to increase employee cooperation is to ask them to sign a document attesting that they have understood and will abide by your business’ security practices. The document can also mention that should the cybersecurity measures be disregarded, there could be repercussions for the employee involved. All in all, if leadership takes the time to discuss cybersecurity, making it relevant and applicable for all employees, your company is much better equipped against a potential security threat.
Invest in Cybersecurity Measures
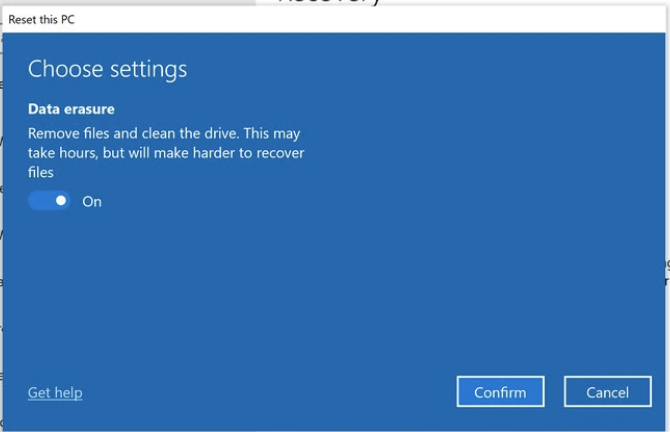
If your mid-size company has yet to invest in cybersecurity measures, there’s no better time than the present to start protecting your valuable information and data. It’s not difficult to get started — begin by setting up a firewall that serves as a barrier between your sensitive information and potential hackers or intruders. In a time when remote workers are becoming more common, your company’s “work from home” staff should also implement a firewall within their personal networks. After all, they regularly access the same important information and data as your in-office employees. Consider providing remote workers with a complementary firewall to eliminate any potential hacking risks.
It’s worth noting that many businesses now allow employees to BYOD (“bring your own device”) to work. In this regard, BYOD calls for the same security measures as a remote worker, since your employees likely transport their laptop, tablet, or other electronics to and from the office each day. On top of that, those who bring their own computer to work are probably using it for personal tasks after hours, which increases the chances of a possible breach. Most importantly, employees should respect the cardinal rule of cybersecurity: do not use the same password for multiple sites, especially as a universal password between personal and professional sites. Urge company leadership to enforce automatic security updates on employees’ devices and inform all staff about your password policy.
Consider Using a Password Manager
An effective solution to your company’s password creation and storage problems is a password manager. A password manager helps your business manage your team’s passwords within a centralized digital “vault.” The primary advantage of a password manager is that your business’ IT team can create intricate, long and random passwords for various sites or accounts that employees gain access to just by logging into the password manager. By streamlining password storage, you can make massive amounts of information secure and basically eliminate the need for staff to create their own passwords. This quickly limits the possibility of a cyber attack and keeps company leadership in control of who can access what information.
Ultimately, password managers dramatically improve cybersecurity in businesses. Research shows that employees often keep their sensitive passwords written down on a Post-It note that could easily be accessed by any passing visitor or coworker alike. Reduce the risks of cyber threats both from internal and external sources by implementing a system that keeps track of who logs into company sites and when. Without this kind of accountability, it can be much more difficult to pinpoint the source of a security breach. Gone are the days of the ‘123456’ passwords — reach out to a local IT managed services provider to implement any of the previously mentioned tactics to strengthen your company’s cybersecurity.